IT-as-a-Service
Agio SkySuite
As a startup or small fund, technology is the last thing you want to think about. We make it easy with SkySuite, your IT-as-a-Service solution that delivers a fully hosted infrastructure in the public cloud.
We speak geek.
So you don’t have to.
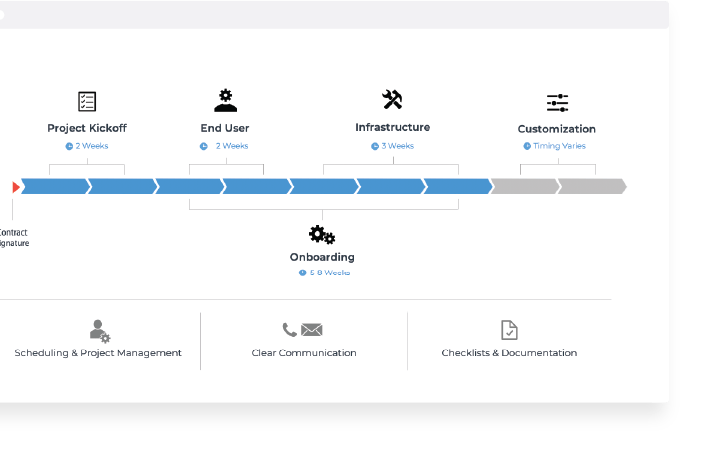
Your to-do list when setting up a hedge fund, private equity, or asset management firm is no small undertaking—you need someone to architect your infrastructure, manage it, and make it easy. Our engineers get that, and we’re here to get you up and running quickly and painlessly.
Unlimited expert guidance.
Proactive reporting.
When you sign on with Agio, we’ll provide over 100 proactive activities throughout the year to ensure your environment is healthy, efficient, and safe. From backups to patching to disaster recovery, our weekly reporting will keep you up to speed.
Instant support.
For those moments when technology just won’t cooperate, our AgioNow Chat gives you and your people instant access to our experts—anytime, anywhere.
Connect with us.
Need a solution? Want to partner with us? Please complete the fields below to connect with a member of our team.
Trending resources.
Are you in?
Find out whether Agio is right for you. Contact us to design a custom solution for your firm.




