Cybersecurity Consulting
Manage risk. Meet requirements. Maximize efficiency.
Not ready to commit? Our one-off consulting engagements let you assess your existing cybersecurity operations without locking in a lifecycle program.
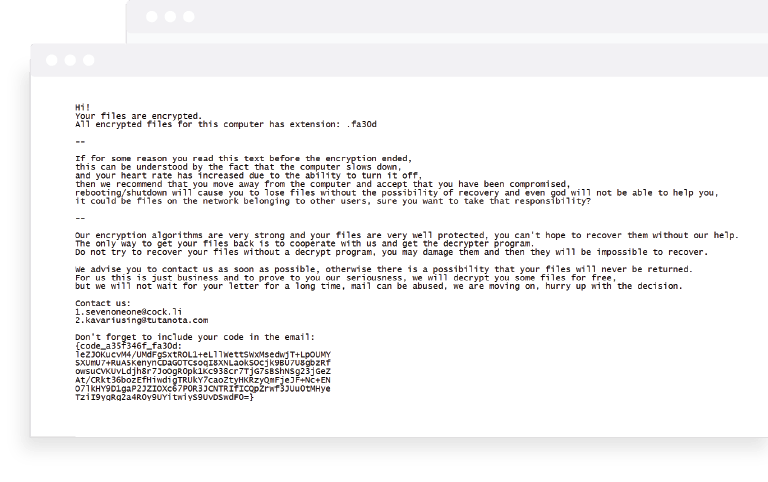
Tackle the unexpected.
Fast-acting defense.
In today’s threat landscape, bad actors can fly under the radar of even the most sophisticated firms. If you suspect your firm has been breached, Agio will deploy an emergency team to execute an incident response plan that includes expert analysis and recommendations for how to contain malicious activity, recover systems, restore data and secure your environment.
Technical Testing
Penetration Tests
Agio’s penetration testing experts evaluate the security of your IT assets from the vantage point of a malicious hacker.
Vulnerability Assessments
The persistence of software vulnerabilities requires an ongoing, systematic approach to testing, evaluation, prioritization, and remediation.
Configuration Management
Security misconfigurations are among the most frequently exploited vulnerabilities. While common, these errors can leave your organization open to serious risks.
Other ways to test us out.
Security Risk Assessment
Through technical, policy, and procedural lenses, we review your information security maturity to determine your level of preparedness in the event of a cybersecurity attack.
Remote Penetration
Testing
We expose the chinks in your armor by looking at your security posture from an attacker’s perspective.
Office 365 Assessment
We review your Office 365 setup to ensure the most up-to-date security features are properly configured.
Policy Development (SEC, HIPAA, PCI, GDPR)
Agio helps you write and review cybersecurity policies based on industry trends and external threats. As the regulatory landscape shifts, we recommend policy enhancements.
Social Engineering Testing
To abate internal threats, we test your team’s response to phishing, pretexting, and USB drive baiting. We also evaluate security in your physical office space.
Ransomware Resiliency
Testing
Agio will perform breach emulations to determine if your existing security controls can successfully detect and defend against increasingly sophisticated ransomware attacks.
Endpoint Testing
Test your end-point solution to ensure it’s proactively protecting your workforce and their various devices while they work from anywhere.
Security Architecture Review
This evaluation determines if your current security architecture is configured to best practice. The results yield a report with specific recommendations for improvements.
End-User Cybersecurity Awareness Training
It’s easier to hack the human than hack the system. Agio’s seminar leverages industry average results and trend analysis to educate your end users on how to spot and evade an attack.
SOC Assessment
With firms making swift and significant changes to their infrastructure and technology, we assess the validity and resiliency of your security operations center for vulnerabilities and gaps.
Cloud Pen Testing
With hundreds of configurations, migrating to the cloud is no simple feat. We test your virtual servers and infrastructure to ensure your Azure-based environment is airtight.
Connect with us.
Need a solution? Want to partner with us? Please complete the fields below to connect with a member of our team.
Trending resources.
Are you in?
Find out whether Agio is right for you.
Contact us to design a custom solution
for your firm.