Phishing Protection
Your holistic, AI-driven solution to protect end users from the #1 cyber-threat.

Don’t get hooked.
Because phishing continues to be dangerous and increasingly sophisticated, we invested in a standalone solution with cutting-edge technology that evolves with hackers and the threat landscape.
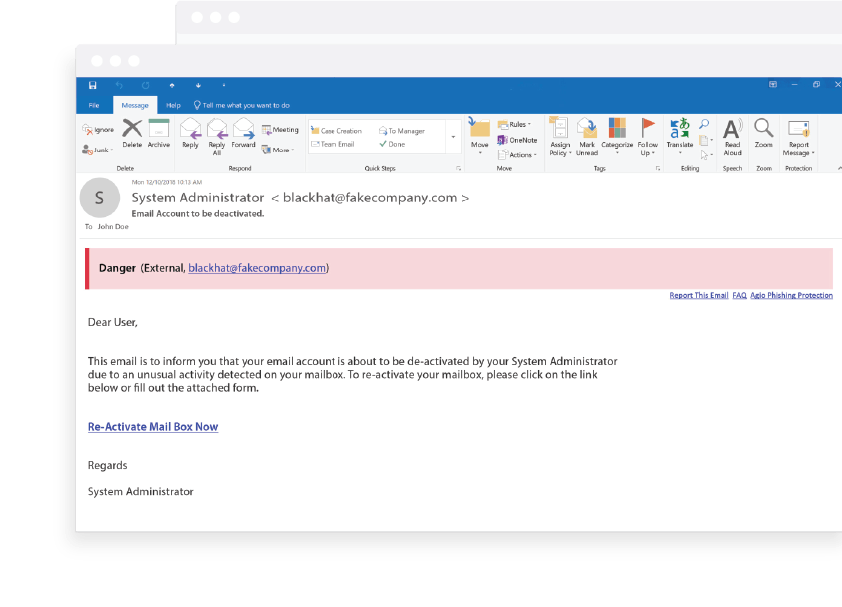
Detection in action.
Our effortless implementation ensures you and your end users can continue business—and performance—as usual. Here’s what you see when you receive a dangerous email.
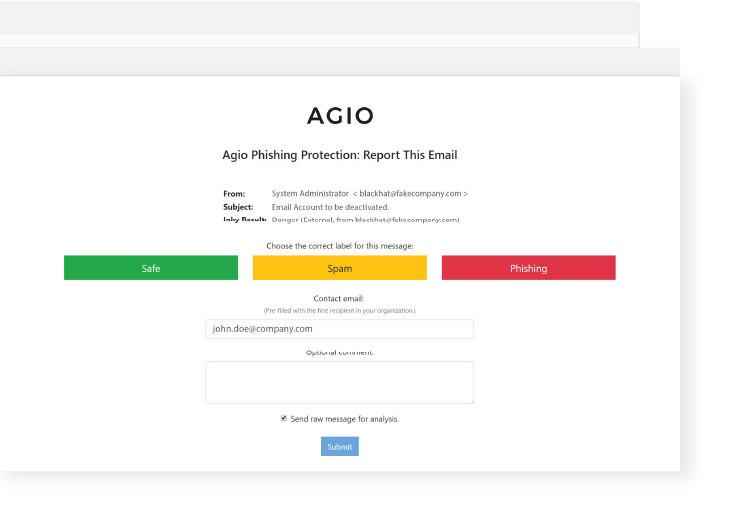
Protection in two clicks.
If your email is classified wrong, or if you want to confirm accuracy, click the “Report This Email” link in the bottom right corner of the banner, which takes you to a web form where you can indicate whether the message is truly Safe, Spam, or Phishing.
Connect with us.
Need a solution? Want to partner with us? Please complete the fields below to connect with a member of our team.
Trending resources.
Are you in?
Find out whether Agio is right for you. Contact us to design a custom solution for your firm.