The post Operational Risk Management: Why Your Firm Needs Regular IT Infrastructure Assessments first appeared on Agio.
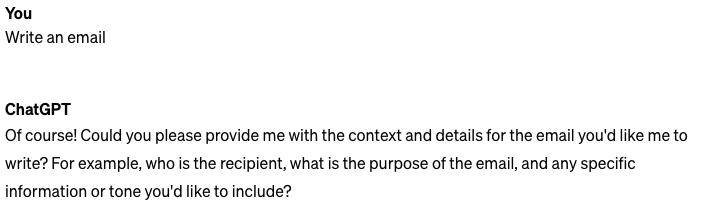
]]>But how will you know when downtime could hit your firm? How do you know if your IT infrastructure has vulnerabilities and bad configurations?
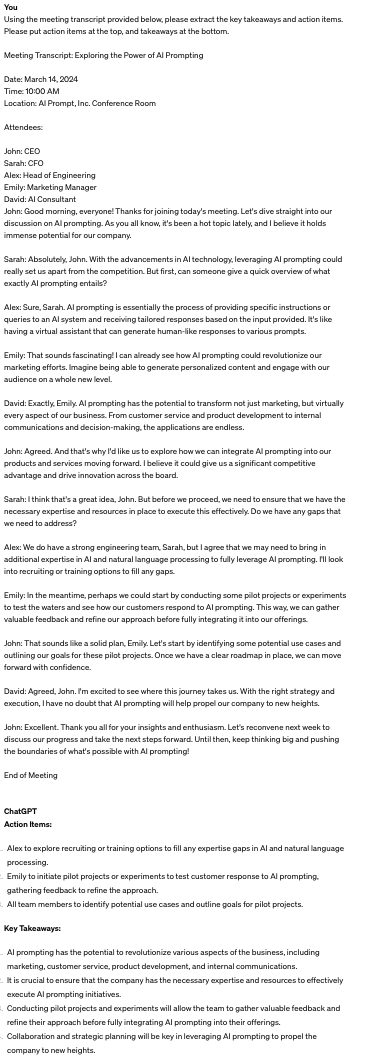
The answer? Regular IT assessments. These assessments offer insights into the health of your IT systems, pinpoint potential vulnerabilities, and recommend necessary improvements. By conducting regular IT assessments, you can proactively mitigate risk, prioritize in-house operations, and protect your reputation and assets. In short, IT assessments are what take you out of a bad IT environment, and into an optimal one, minimizing downtime that can disrupt critical operations.
Read on to explore why IT assessments are a must-have for your firm, exploring their benefits and practical implementation strategies.
Risks of Neglecting IT Assessments
Whether you’re new to managing the technology in your organization or simply haven’t checked in for a while, that unknown territory can be a dangerous blind spot.
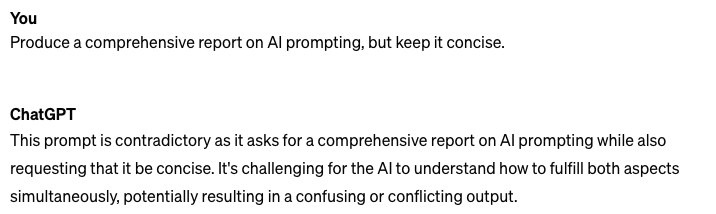
Without a clear understanding of your technical architecture, configuration, and security posture, you’re leaving your business exposed to a host of potential pitfalls. Is your infrastructure aligned with industry best practices? Do you have any unknown vulnerabilities lurking in your systems? The lack of visibility can be a ticking time bomb. Below are the risks for neglecting IT assessments.
Outdated or inadequate technology infrastructure:
- Impact of operational efficiency and productivity: Neglecting IT assessments can result in maintaining outdated or inadequate technology infrastructure. This can hinder your firm’s operational efficiency and productivity, as obsolete systems may not be able to keep up with the demands of modern investment management practices. Slow software, outdated hardware, and inefficient processes can all contribute to wasted time and resources.
- Potential for system failures or downtimes: Without regular IT assessments, there’s a higher likelihood of experiencing system failures or downtimes, which can disrupt critical operations such as trading, portfolio management, and client communication. These disruptions not only impact productivity but also damage client trust and satisfaction.
Cybersecurity vulnerabilities:
- Risk of data breaches and cyber-attacks: Neglecting IT assessments leaves your firm vulnerable to cybersecurity threats, including data breaches and cyber-attacks. Outdated security measures and inadequate defenses make it easier for hackers to exploit vulnerabilities and gain unauthorized access to sensitive information. The consequences of a data breach can be severe, resulting in financial losses, reputational damage, and legal liabilities.
- Compliance issues and regulatory penalties: Failing to address cybersecurity vulnerabilities through regular IT assessments can lead to compliance issues and regulatory penalties. Investment management firms are subject to stringent regulations regarding data protection and information security. Non-compliance not only exposes your firm to legal risks but also undermines trust with clients and regulatory authorities.
Competitive disadvantage:
- Inability to leverage cutting-edge technologies: By neglecting IT assessments, your firm may fall behind competitors who invest in updating their technology infrastructure regularly. Failing to leverage cutting-edge technologies such as artificial intelligence, machine learning, and data analytics can put you at a competitive disadvantage, limiting your ability to innovate and deliver value to clients.
- Challenges in attracting and retaining top talent: Top talent in the investment management industry seeks opportunities to work with firms that prioritize technology and innovation. Neglecting IT assessments signals to potential employees that your firm may not be committed to staying ahead of the curve. This can be challenging to attract and retain top talent, further exacerbating your competitive disadvantage in the market.
Benefits of Regular IT Assessments
An in-depth IT infrastructure assessment can shed light on the critical details you’re missing, providing a comprehensive report of your findings and the necessary remediation steps. Here’s what you can get out of an IT assessment.
Clear view of any technology gaps:
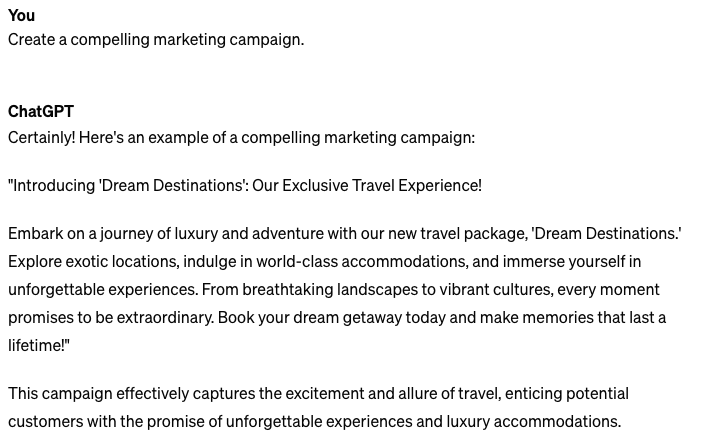
Regular IT assessments allow your firm to address technology gaps. By conducting these assessments, your firm will stay competitive and agile as technology continues to progress with new SEC regulations and AI advancements.
- Ensuring alignment with industry best practices: Through regular IT assessments, you can benchmark your IT infrastructure against industry best practices and standards. This ensures that your systems are up-to-date and compliant with regulations, reducing the risk of non-compliance penalties and reputational damage.
- Optimizing resource allocation and budgeting: By identifying areas of inefficiency or redundancy in your IT systems, you can optimize resource allocation and budgeting. You can reallocate resources to areas that provide the most value to your firm and your valued employees, whether it’s upgrading critical infrastructure or investing in new technology to gain a competitive edge.
Enhanced cybersecurity posture:
Cybersecurity is a top priority for investment management firms, given the sensitive nature of the data they handle. Regular IT assessments are essential for enhancing your firm’s cybersecurity posture, helping you identify and mitigate vulnerabilities before they can be exploited by malicious actors.
- Identifying and mitigating vulnerabilities: Through thorough assessments of your IT systems, you can identify potential vulnerabilities and weaknesses in your cybersecurity defense. This allows you to take proactive measures to mitigate these risks, whether it’s patching software vulnerabilities, implementing multi-factor authentication or forming stronger network security protocols.
- Implementing robust security measures: Regular IT assessments provide valuable insights into the effectiveness of your firm’s security measures. This enables you to implement robust security controls and protocols to protect against emerging threats, guard your firm’s sensitive data and maintain client trust.
Improved operational efficiency:
In addition to focusing on security, regular IT assessments also contribute to improving operational efficiency within your investment management firm. By emphasizing data-driven decision-making and strengthening internal systems, these assessments help you maximize productivity and drive business growth.
- Streamlining processes and workflows: IT assessments identify bottlenecks and inefficiencies in your firm’s processes and workflows, allowing you to streamline operations and eliminate unnecessary steps. The overall productivity and makes sure that your firm operates at peak efficiency.
- Enabling data-drive decision-making: By evaluating the performance of your IT systems and analyzing key metrics and data points, IT assessments underscore data-driven decision-making within your firm.
Regular IT assessments are instrumental in guaranteeing the alignment of investment management firms with the cybersecurity and managed IT fields, optimizing resource allocation, and fortifying cybersecurity measures. By streamlining processes, enhancing data-driven decision-making, and prioritizing operational efficiency, these assessments lay the foundation for sustained technological growth.
Key Areas to Assess
When evaluating a managed service provider to conduct your IT infrastructure assessment, it’s important to ensure they assess the following areas.
Network and Assets:
A proper IT infrastructure assessment should scan your environment outside of any Remote Monitoring and Management (RMM) tools to discover all assets. This includes evaluating server and network infrastructure for scalability and resilience, as well as assessing end-user devices and peripherals to support your investment management operations.
On-Premises Architecture:
You’ll also want the IT assessment to check the configuration of on-premises systems; VMware, physical servers, SAN and storage and document the configuration and compare to best practices, highlighting any areas that require attention.
Software and applications:
Evaluation of software and applications is crucial for optimizing functionality and efficiency. You must update your core investment management, particularly in sectors like finance where security and accuracy are vital.
Cloud Architecture and Configuration
Primarily focused at Azure and AWS, the assessment will review how the cloud environment has been deployed in the following areas.
- Cloud Architecture: How the cloud environment has been set-up and how it aligns to vendor well-architected frameworks including logical design, security, cost optimization and reliablity.
- Policy: How policies have been implemented, how access and systems are controlled by automated methods to control configuration drift.
- Role based access control: Review of administrative and priviledged groups.
Identity
Review Azure Active Directory and ensure all logging has been enabled. Configuration is reviewed to ensure it meets current recommended best practices and modern deployment methods. This is centered around security and Role Based Access Control (RBAC) and end user protection.
Review Active Directory Domain Services; password policy, dormant accounts, RBAC,Active Directory architecture, replication health and best practices.
Office365
End to end review of the Office365 configuration, check for unexpected permissions, mail forwarding rules, send as permissions and review for configuration error.
Nothing to Lose, Everything to Gain
Regular IT assessments are essential for your investment management firm to maintain competitiveness, mitigate risks, and drive operational excellence.
IT is not just a support function but a strategic enabler that fuels growth and innovation within your firm. Investment management firms are urged to prioritize IT assessments.
Agio’s IT Assessment provides the necessary expertise to conduct a comprehensive analysis, flagging potential risks and offering clear reconciliation roadmaps. Skipping this crucial step could result in costly disruptions and inefficiencies during the migration process. By partnering with Agio and committing to regular IT assessments, your firm can fortify its resilience, adaptability, and long-term success. Contact us today.
The post Operational Risk Management: Why Your Firm Needs Regular IT Infrastructure Assessments first appeared on Agio.
]]>